When your auditor asks "show me the approval trail for that automated data transfer," the last thing you want is a panicked search through email threads, scattered spreadsheets, and tribal knowledge. Yet this is exactly where most Canadian organizations find themselves when automation meets compliance requirements. The problem isn't automation itself—it's that most workflows are built for speed and efficiency, with compliance bolted on as an afterthought. The good news? You can design automation audit logs and approval mechanisms directly into your workflows, creating a single source of truth that satisfies both PIPEDA and FIPPA requirements without drowning your team in manual documentation.
Why Traditional Logging Fails Compliance Requirements
Spreadsheets were never designed to be audit systems. They lack version control, can be edited without trace, and provide no cryptographic proof of when actions occurred. When a municipal government in Ontario faced a FIPPA access request regarding automated constituent communications, their Excel-based tracking system couldn't definitively prove which records had been processed or when citizen consent was captured. The resulting investigation took three months and significant legal costs.
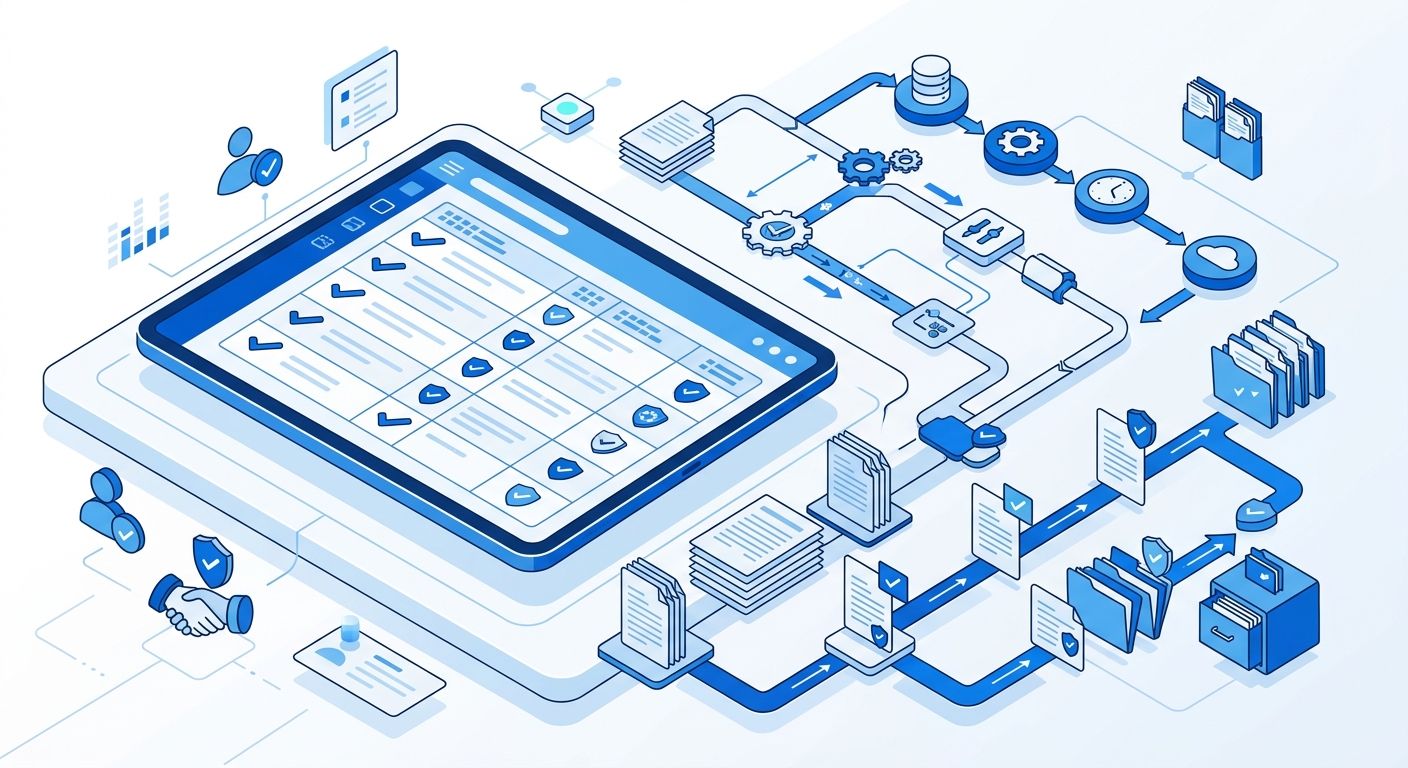
Compliance-ready workflows require immutable logs—records that can't be altered retroactively and contain complete contextual information. This means capturing not just what happened, but who authorized it, what data was involved, when the action occurred, and what the system state was at that moment. Manual logging systems simply can't maintain this level of rigour across hundreds or thousands of automated executions.
Modern automation platforms can generate these logs automatically, but only if you design your workflows with evidence collection in mind from day one. The key is thinking like an auditor before you build, not after you're served with a compliance notice.
The Four Pillars of Audit-Friendly Automation
Building PIPEDA automation evidence into your workflows requires addressing four fundamental requirements. First, you need immutable execution logs that capture every workflow run with timestamps, input data, decision points, and outcomes. These logs should be write-once and stored in a system with tamper detection.
Second, implement embedded approval gates that require human authorization at critical points. A healthcare network in British Columbia redesigned their patient data automation to require explicit approval before any cross-system transfers. Each approval is logged with the authorizer's identity, timestamp, and the specific records they reviewed—creating an unbreakable chain of custody.
Third, ensure data lineage tracking that shows how information transforms as it moves through your automation. When FIPPA record keeping requirements mandate knowing exactly what personal information was processed, you need logs that capture input states, transformation logic, and output results for every step.
Finally, build in exception handling with evidence capture. When something goes wrong, your automation should log the failure state, preserve the data context, and trigger appropriate notifications—all while maintaining the evidence chain. This turns errors from compliance risks into documented, manageable events.
Designing Your Compliance Logbook Architecture
Start by mapping your workflow's compliance touchpoints. For each automation step that processes personal information, makes a decision, or crosses a system boundary, ask: "What would an auditor need to see here?" This creates your logging specification before you write a single workflow node.
A financial services company in Toronto used this approach when automating their credit application review process. They identified twelve compliance touchpoints, including consent verification, credit bureau data access, automated decision logic, and final human approval. Each touchpoint now generates structured log entries containing the applicant ID, the specific data accessed, the decision or action taken, and supporting evidence like consent timestamps or approval signatures.
Your log schema should capture minimum viable evidence: workflow execution ID, timestamp (with timezone), triggering event or user, input data (or references to it), processing logic applied, output or decision, and any errors or exceptions. Store these logs in a dedicated system separate from your operational databases—this separation prevents accidental deletion and clearly designates logs as compliance records with appropriate retention policies.
Consider implementing cryptographic signing for critical log entries. When each log record includes a hash of its content signed by your automation system, you create mathematically verifiable proof that records haven't been tampered with—a powerful safeguard during disputes or legal proceedings.
Building Approval Workflows That Document Themselves
Automation doesn't mean eliminating human oversight—it means making oversight more effective and automatically documented. Design approval gates that pause workflow execution and require explicit human decisions at predetermined points. A provincial government agency automated their FIPPA access request processing but built in three approval stages: initial classification by privacy officers, data extraction review by records managers, and final release authorization by legal counsel.
Each approval stage in their workflow captures who approved what, when they approved it, what information they reviewed, and any comments or conditions they attached. This creates a self-documenting approval chain that satisfies audit requirements without requiring staff to maintain separate documentation systems.
Your approval mechanism should integrate with your organization's authentication system to capture verified identities, not just usernames. It should present approvers with the specific context they need—sample records, risk assessments, compliance checklists—and log what information was displayed during the approval process. This proves not just that approval was given, but that it was informed approval based on complete information.
Operationalizing Compliance Evidence Collection
The most sophisticated logging architecture fails if your team can't easily access and use the evidence when needed. Build reporting interfaces that let compliance officers query logs by date range, data subject, workflow type, or specific processing activities. A healthcare organization created a simple dashboard where privacy officers can enter a patient ID and instantly retrieve every automated processing event involving that patient's data—complete with timestamps, authorizations, and data transformations.
Your evidence collection system should also support proactive compliance monitoring. Set up automated alerts when workflows execute without proper approvals, when processing volumes exceed expected thresholds, or when error rates suggest potential compliance issues. This shifts compliance from reactive audit response to proactive risk management.
Consider generating automated compliance reports that aggregate log data into audit-ready formats. Monthly summaries showing processing volumes by data type, approval turnaround times, exception rates, and access patterns give leadership visibility into compliance posture while creating a paper trail that demonstrates ongoing diligence.
Document your logging and approval architecture itself. Create clear specifications showing what gets logged where, how long logs are retained, who has access, and how evidence is retrieved during audits. This metadata about your compliance system is often as important during audits as the logs themselves.
Making Compliance a Competitive Advantage
Organizations that build compliance-ready workflows from the ground up don't just reduce audit risk—they move faster. When your automation includes built-in logging and approval mechanisms, you eliminate the friction of post-hoc documentation and the fear of compliance violations that slows down innovation.
A Canadian e-commerce platform rebuilt their customer data automation with comprehensive audit logging and found that their time-to-market for new features actually decreased. Developers no longer worried about compliance implications because the logging infrastructure handled evidence collection automatically. Product managers could confidently approve data processing changes knowing the approval trail was automatically preserved.
This is the hidden value of audit-friendly automation: it removes compliance from being a brake on innovation and transforms it into infrastructure that enables confident, rapid deployment. Your automation audit logs become not just protection against audits, but documentation that proves your organization's commitment to responsible data handling—a genuine competitive advantage in an environment where data breaches and privacy violations regularly make headlines.
Ready to ensure your automations can withstand scrutiny? Integratie's compliance automation experts can review your current workflows, identify logging gaps, and design audit-ready evidence collection that satisfies PIPEDA, FIPPA, and industry-specific requirements. Book a compliance audit of your current automations and transform compliance from a risk into a documented strength.